In this blog we will share how to use Keycloak for Identity and Access Management — but first, here are some frequently asked questions about Keycloak.
What is Keycloak?
Keycloak is an open source Identity and Access Management tool with features such as Single-Sign-On (SSO), Identity Brokering and Social Login, User Federation, Client Adapters, an Admin Console, and an Account Management Console. It simplifies the process of adding authentication to applications and securing services with minimum effort. Keycloak plays a crucial role in helping authenticate users across different applications, ensuring a seamless and secure user experience.
Is Keycloak free?
Yes, Keycloak is free. The Keycloak server is open source and distributed under the Apache License 2.0, making it a compelling choice for organisations seeking full control over their identity and access management infrastructure without commercial licensing costs.
IAM (Identity and Access Management)
IAM — or IdM (Identity Management) — is a framework for authenticating user identity and managing user privileges. It determines whether users have access to the files, networks, and resources they request, and governs how and by whom information can be accessed or modified. IAM systems provide administrators with tools and technologies to manage user roles, track user activity, enforce access policies, and maintain a complete audit trail of identity-related events.
https://www.youtube.com/watch?v=GHy2KFjlhpg
Identity Management has four main functions:
- The pure identity function: The creation, management, and deletion of identities, without regard to access entitlements.
- The user access (log-on) function: Controlling how users authenticate to services — for example, using a smart card and its associated data to log on to an application.
- The service function: Delivering personalised, role-based, on-demand, multimedia, and presence-based services to users and their devices.
- Identity Federation: Enabling a system to authenticate a user across organisational boundaries without requiring knowledge of that user's password, using federated identity standards.
Single Sign-On and User Management
Single Sign-On (SSO) is an access control property that allows users to log in once with a single set of credentials and gain access to multiple related, independent software systems — without needing separate usernames or passwords for each. SSO is typically implemented over Lightweight Directory Access Protocol (LDAP), with LDAP databases stored on directory servers. It can also be achieved over IP networks using cookies, provided the sites share a common DNS parent domain.
Common authentication schemes that underpin SSO include OAuth 2.0, OpenID, OpenID Connect (OIDC), and social login providers such as Facebook Connect. Unlike traditional authentication — where users must re-enter credentials every time they access a new application — SSO allows users to authenticate once and remain signed in across all connected systems for the duration of their session.
Benefits of using SSO
- Reduces the risk of credential exposure through third-party sites.
- Reduces password fatigue caused by managing multiple username and password combinations.
- Reduces time spent re-entering passwords for the same identity across applications.
- Reduces IT helpdesk calls related to forgotten passwords, lowering overall IT support costs.
Keycloak Authorization
Keycloak Authorization Services is a pivotal feature that enables fine-grained authorization policies, enhancing Keycloak's open source identity and access management solution. This service facilitates the implementation of detailed access control mechanisms, including Attribute-Based Access Control (ABAC) and Role-Based Access Control (RBAC), to manage permissions and authorization for applications and services comprehensively. Users authenticate with Keycloak rather than with individual applications directly, eliminating the need for each application to handle its own login forms, user authentication logic, and user data storage.
Once logged in to Keycloak, users don't have to log in again to access different applications — and the same convenience applies to signing out. Keycloak provides everything a sophisticated user management platform needs: centralized authentication, system security, social logins, mobile app support, and seamless integration with existing solutions. Access to resources is governed by configurable default policies and permissions, streamlining the authorization process across the entire application landscape. Keycloak also supports LDAP and Active Directory integrations out of the box.
Password Policies
By default, each new realm in Keycloak is created without any password policies, meaning users can set passwords of any length or complexity. While this is acceptable in development or learning environments, it is not suitable for production deployments. Keycloak's password policy settings allow administrators to enforce minimum length, complexity requirements, history constraints, and expiration rules to meet organisational security standards.
OTP to Authenticate Users
Keycloak supports One-Time Password (OTP) authentication and includes a range of configurable policies for use with Google Authenticator and FreeOTP. Two OTP types are supported:
- TOTP (Time-Based OTP) — generates a new code every 30 seconds based on the current time.
- HOTP (Counter-Based OTP) — generates a new code based on a counter that increments with each use.
Client Certificate
- A client authentication certificate is used to authenticate clients during an SSL/TLS handshake. It is presented by the client to the server at the start of a session, as opposed to a server certificate, which flows in the other direction. A client certificate typically contains a digital signature, expiration date, client name, Certificate Authority (CA) name, revocation status, SSL/TLS version number, and serial number — all structured using the X.509 standard.
- Major web browsers including Firefox, Chrome, Safari, and Edge support client certificates. To integrate an application with Keycloak using certificate-based authentication, administrators must configure the relevant client settings in the Keycloak Admin Console — specifically enabling or disabling client authentication, defining the authentication flow, and setting the permitted login paths.
- When client certificate authentication is enabled, only users connecting from a client application loaded with a valid, matching certificate will be granted access. Even users with correct credentials (username and password) will be denied if their client does not present the required certificate.
- In practice, if a user connects from a browser without the correct client certificate installed, the login page itself may fail to load entirely.
- To summarise the distinction: a server certificate is sent from the server to the client at session start, and is used by the client to authenticate the server. A client certificate is sent from the client to the server, and is used by the server to authenticate the client.
Keycloak Admin Console Working Procedure
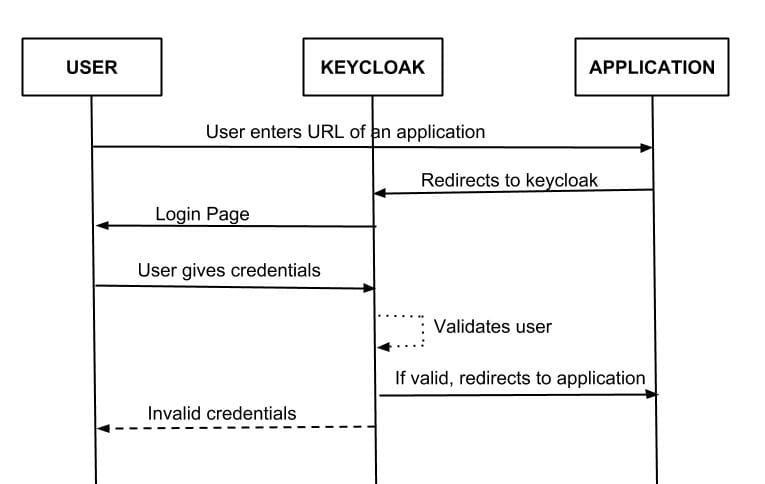
On a system fully secured with Keycloak:
A user clicks a link from a public page to navigate to a protected area of the application. The protected URL is registered in the application's settings within the Keycloak Admin Console.
- The user is redirected to the Keycloak authentication page. After providing their username and password, Keycloak redirects the user back to the application with a short-lived authorization code.
- The application sends this code to Keycloak along with the application's client ID and client secret. Keycloak responds with an Access Token, an ID Token, and a Refresh Token. The application uses the relevant token to evaluate the user's claims, and grants or denies access to the requested protected URL accordingly.
Keycloak With OpenID Connect (OIDC)
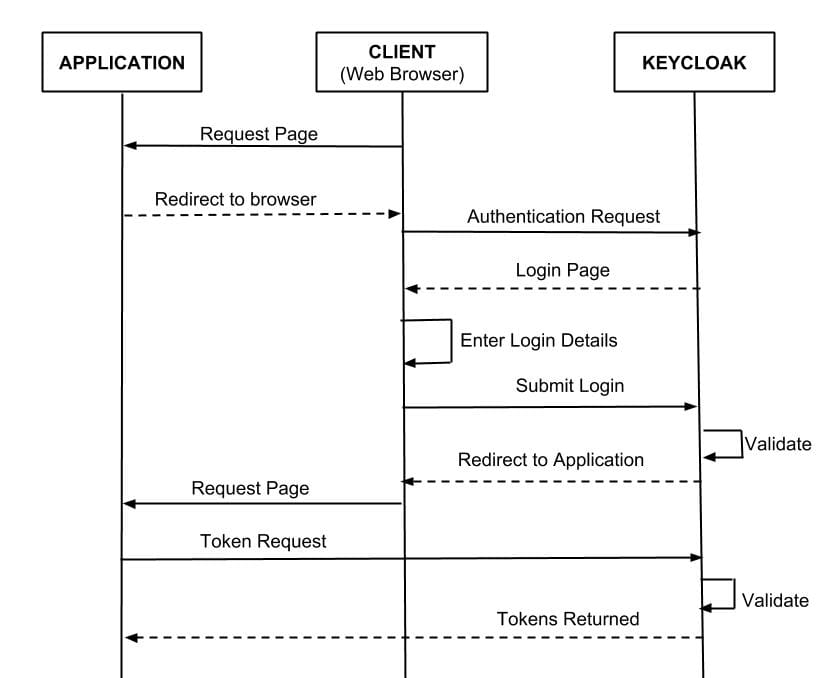
OIDC (OpenID Connect) is an authentication protocol built as an identity layer on top of OAuth 2.0. While OAuth 2.0 is an authorization framework — designed for delegated access rather than authentication — OIDC extends it into a full authentication and authorization protocol by introducing the ID Token: a signed JWT that carries verifiable claims about the authenticated user. The OIDC authentication flow when integrated with Keycloak works as follows:
- The browser visits the application. The application detects that the user is not logged in and redirects the browser to Keycloak for authentication, passing along a callback URL (redirect URL) as a query parameter.
- Keycloak authenticates the user and creates a one-time, very short-lived temporary code. Keycloak then redirects back to the application using the callback URL provided, appending the temporary code as a query parameter.
The application extracts the temporary code and makes a back-channel REST request to Keycloak to exchange it for an identity token, access token, and refresh token. Once this temporary code has been used to obtain the tokens, it is invalidated and cannot be reused — preventing potential replay attacks.
Requirements
The tools required for the integration walkthrough below are:
Operating systems: Windows, Docker
Tools: Maven
Single-Sign-On: Keycloak
Development environment: Eclipse
Programming language: Java
https://www.youtube.com/watch?v=sTaHHtSkF0A
Integrating Multiple Applications with Keycloak
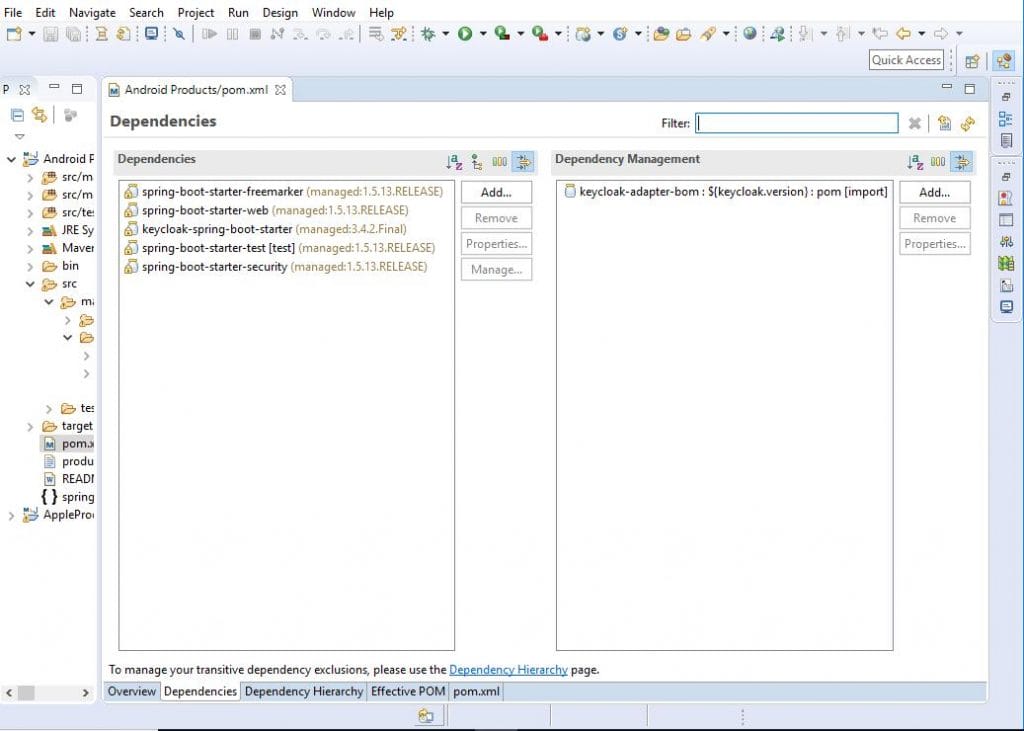
- Add a
docker-compose.ymlfile and save it in your project folder.
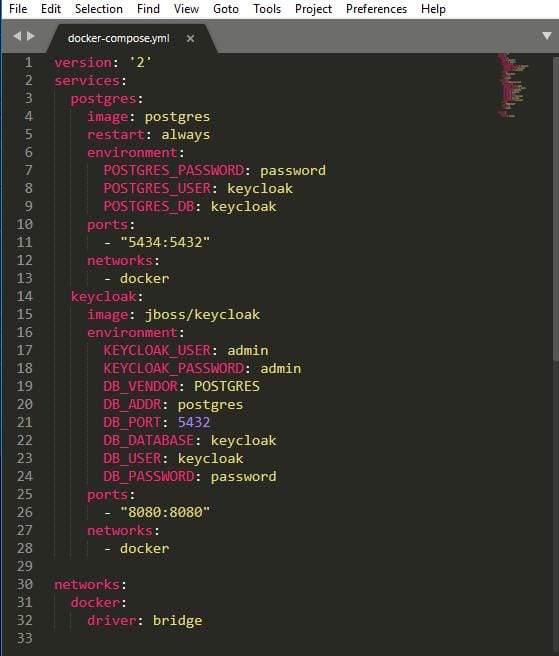
Add the Keycloak and Spring Boot dependencies to your project.
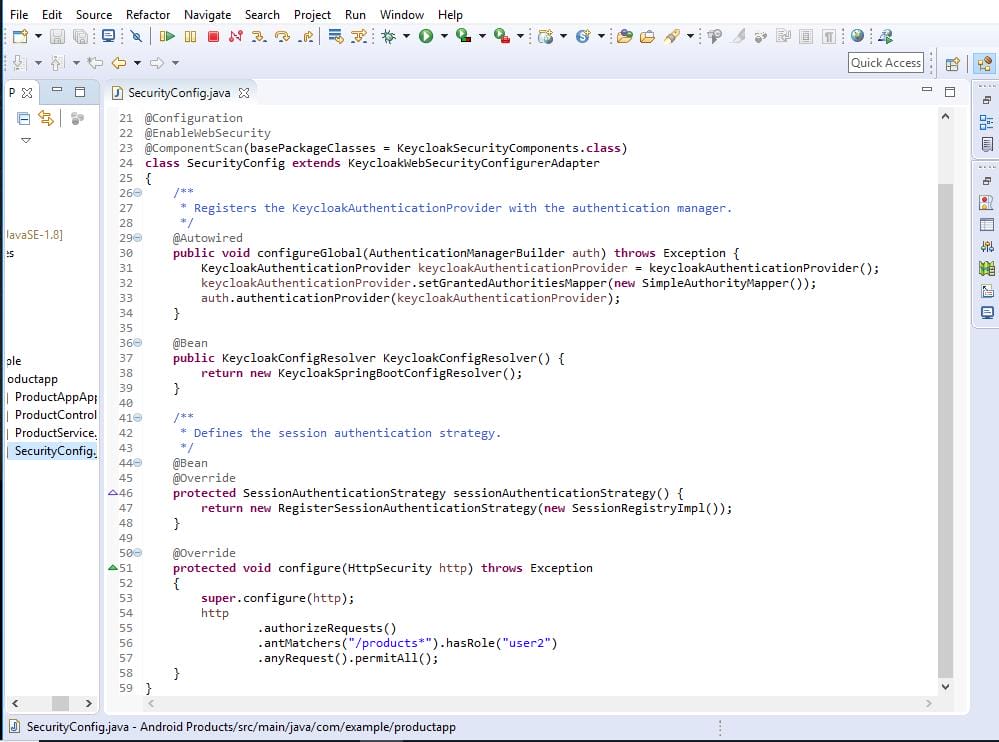
Create a SecurityConfig.java file in your project.
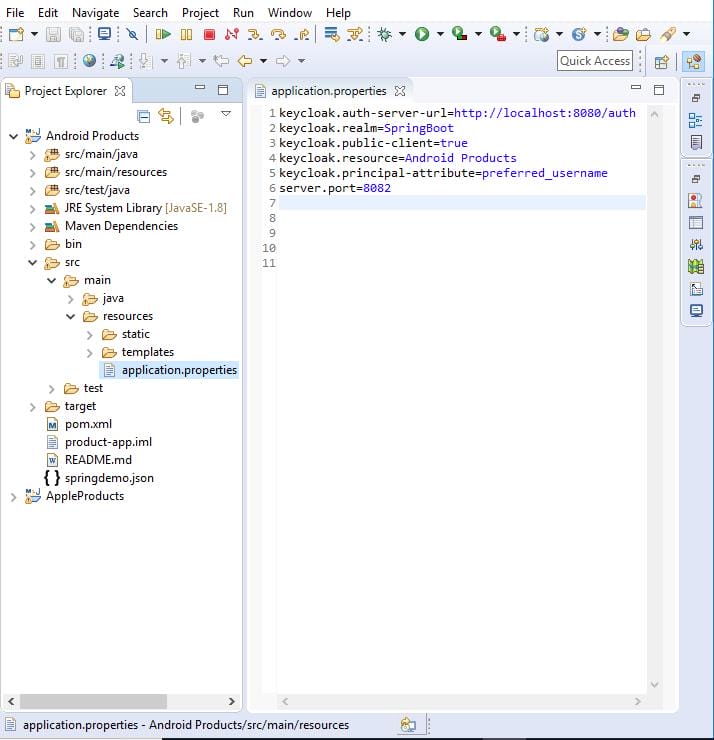
Create an application.properties file with your Keycloak configuration.
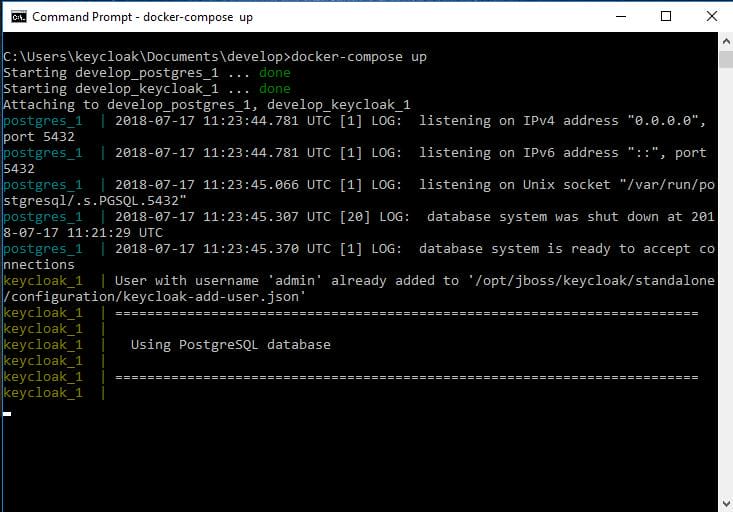
Open a command prompt and run docker-compose up to start Keycloak.
Open your browser, navigate to the Keycloak URL, and click Administration Console.
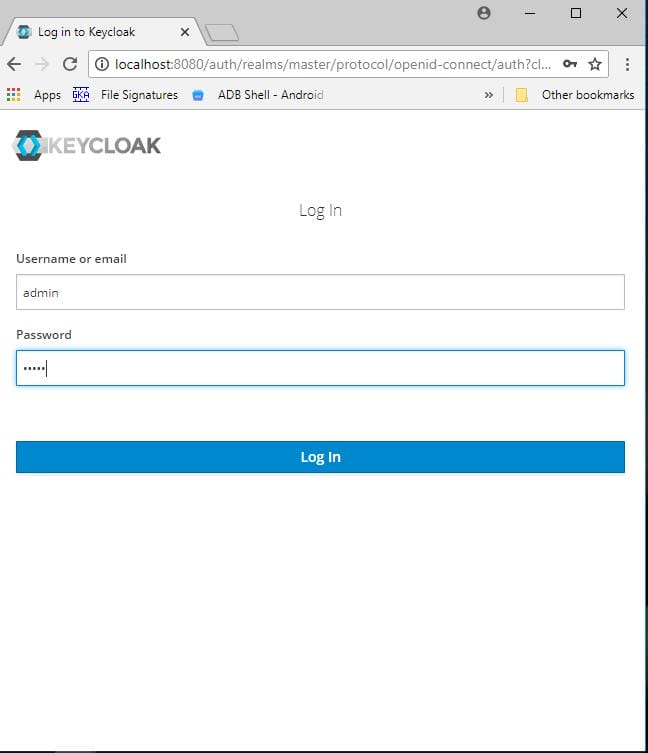
The default username and password are both admin. Change these immediately in any non-development environment.
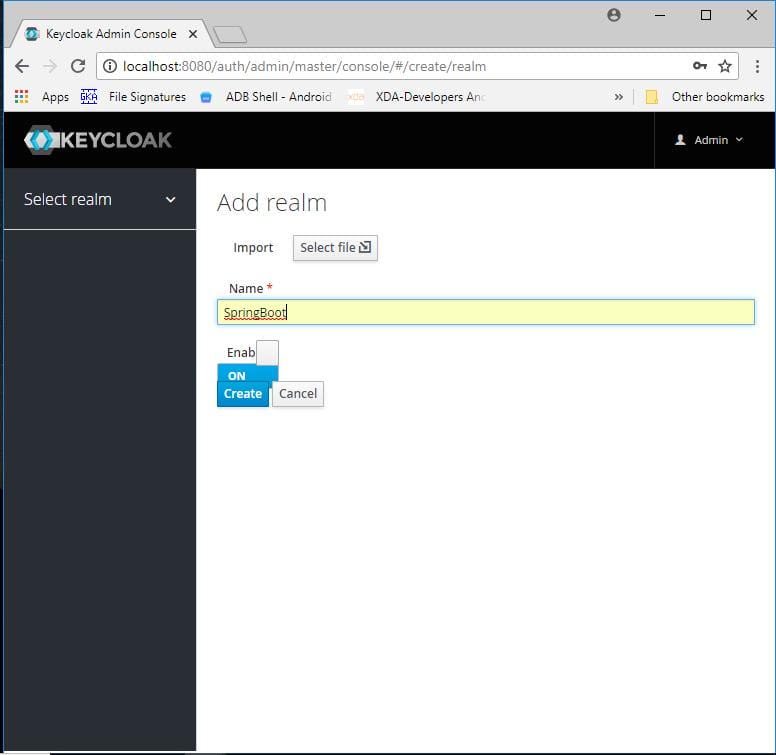
Click Add Realm and give it a name.
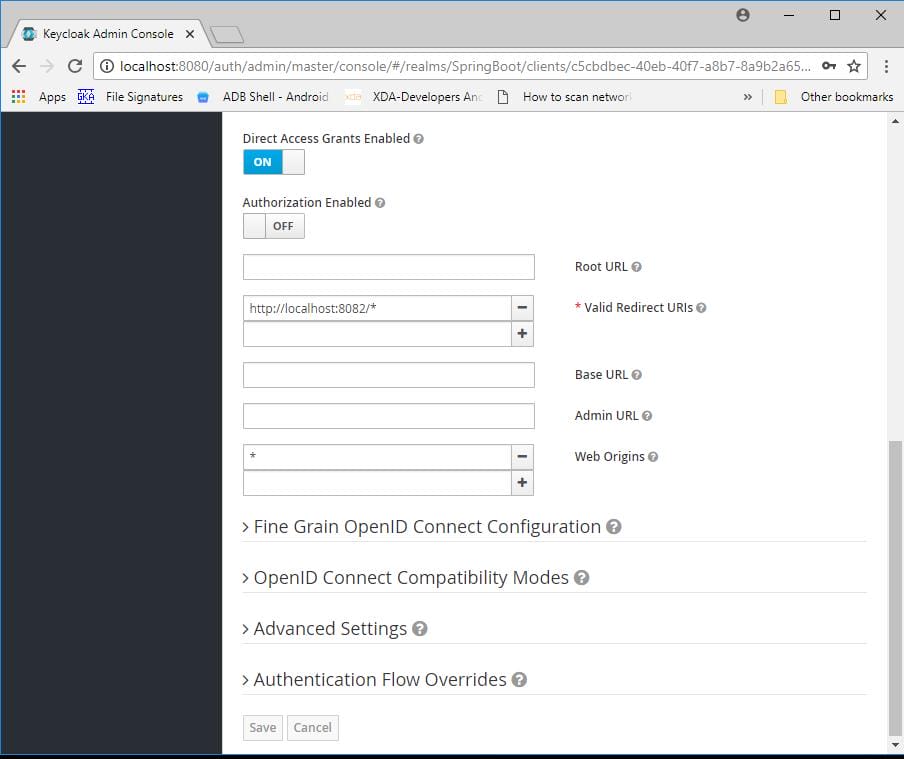
Add a new client.
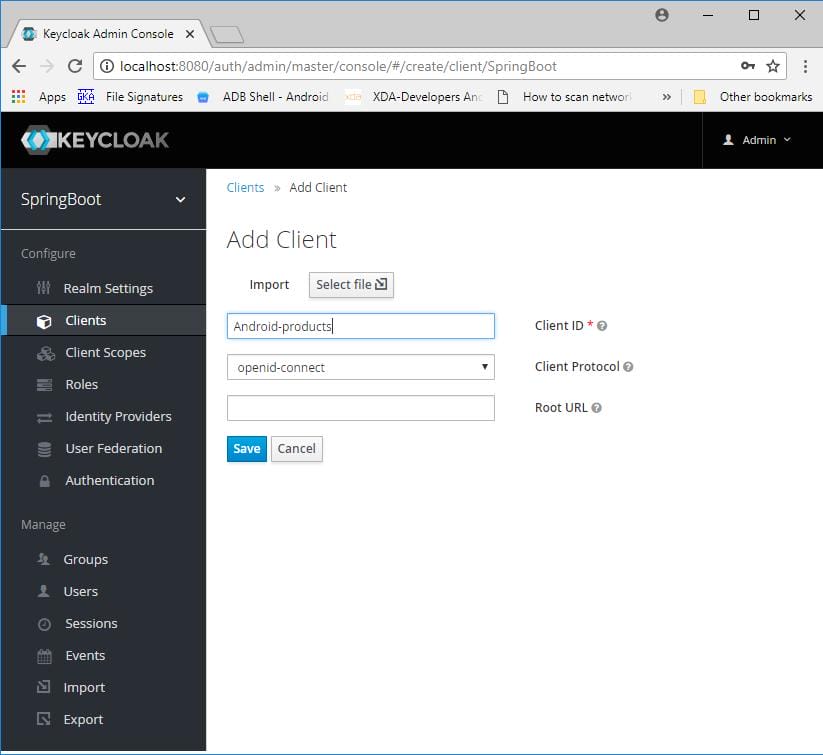
Enter your application's URL in the Valid Redirect URIs field.
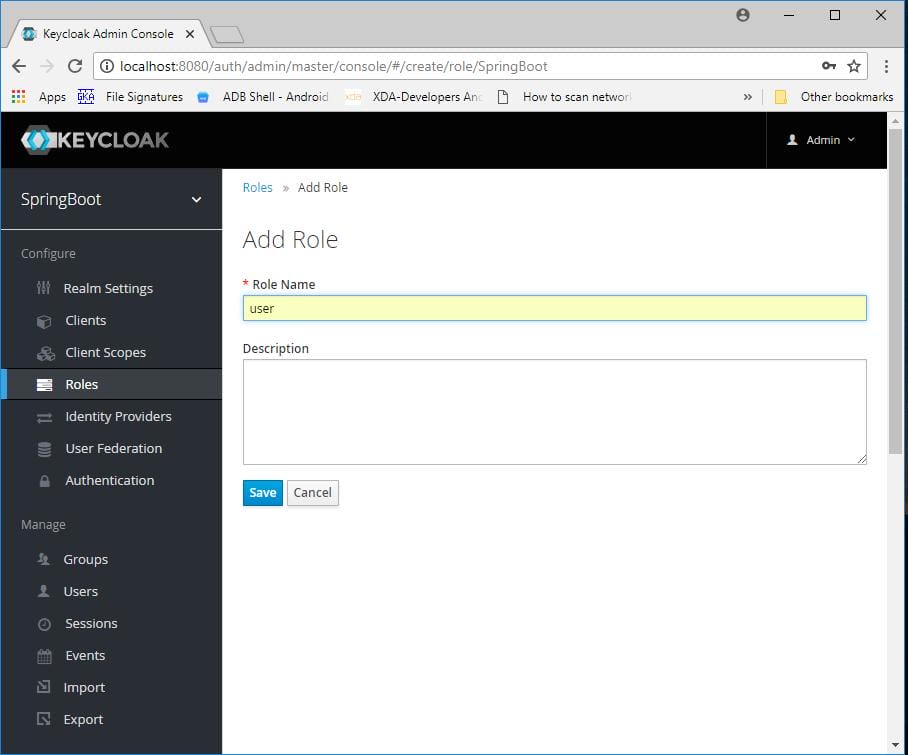
Add a role.
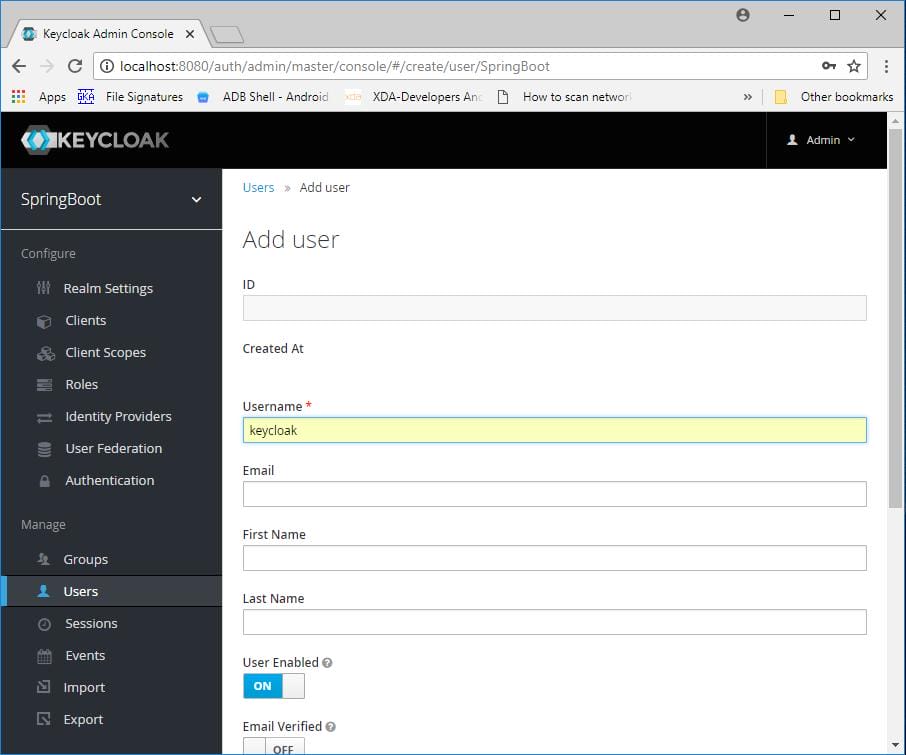
Add a user.
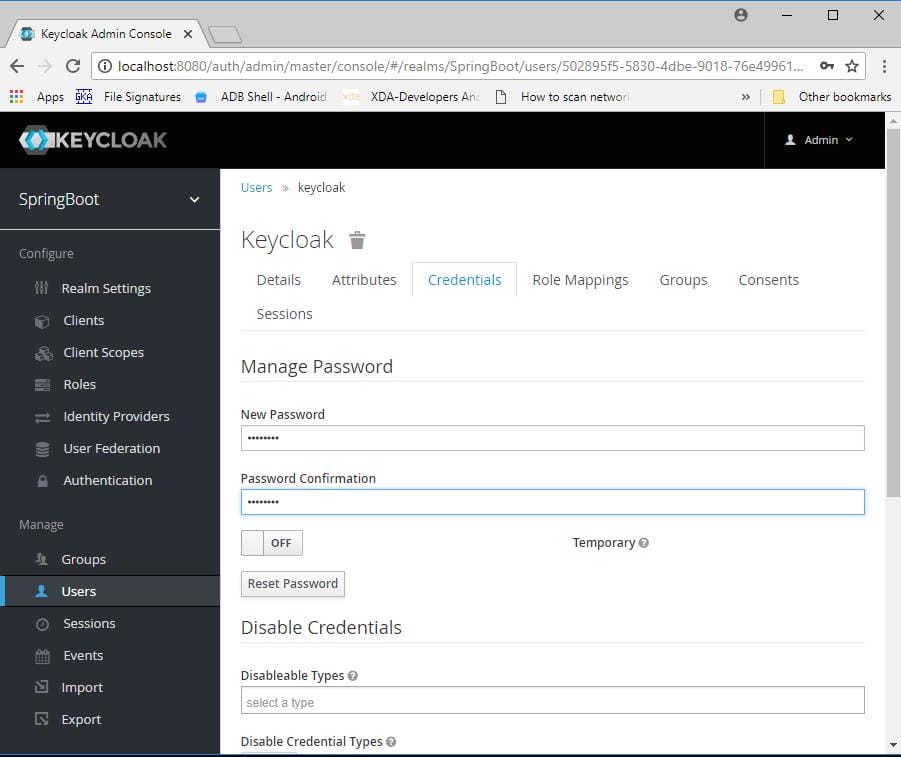
Go to the Credentials tab and set a new password for the user.
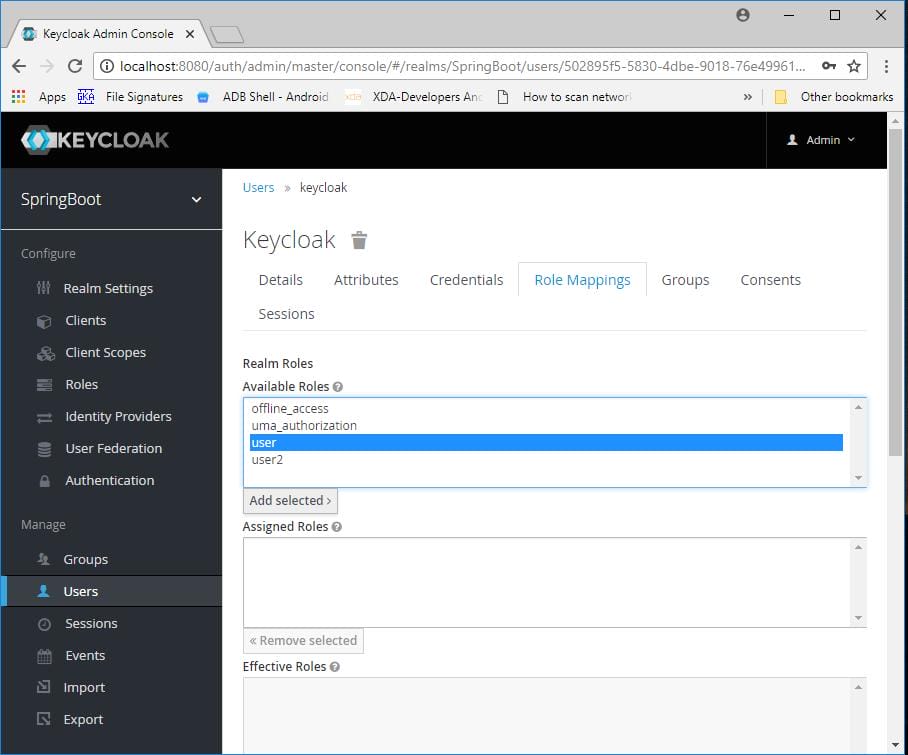
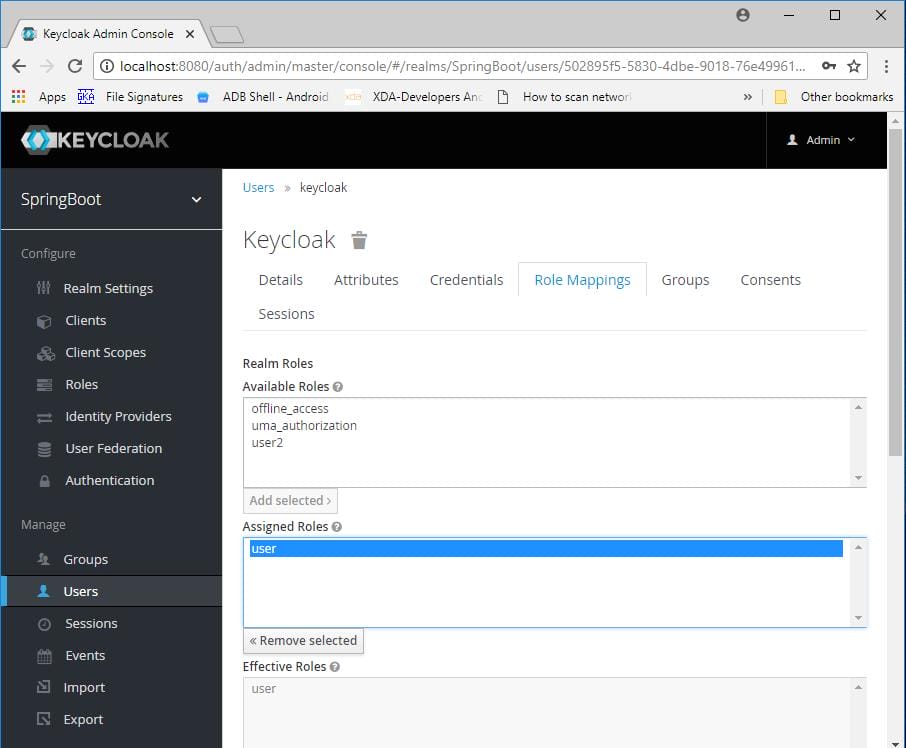
Go to the Role Mappings tab and assign the role to the user.
 Repeat the same steps to configure a second application. Use the same realm, but create a new client, role, and user for the second app.
Repeat the same steps to configure a second application. Use the same realm, but create a new client, role, and user for the second app.
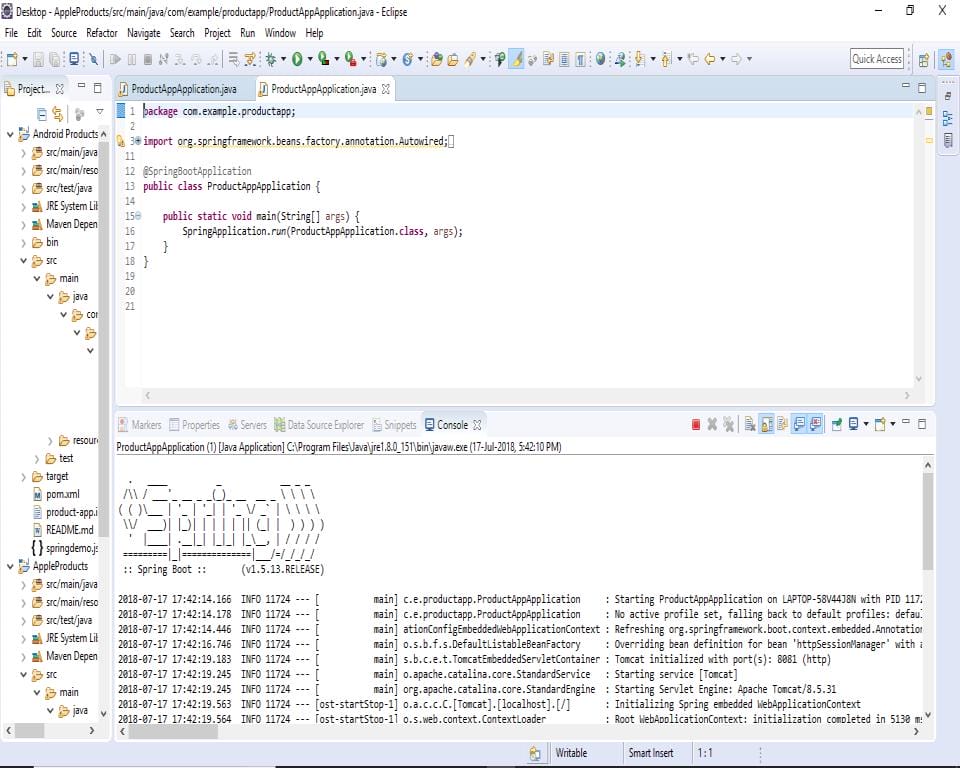
Start both applications.
Open the browser and navigate to the URL for the first application.
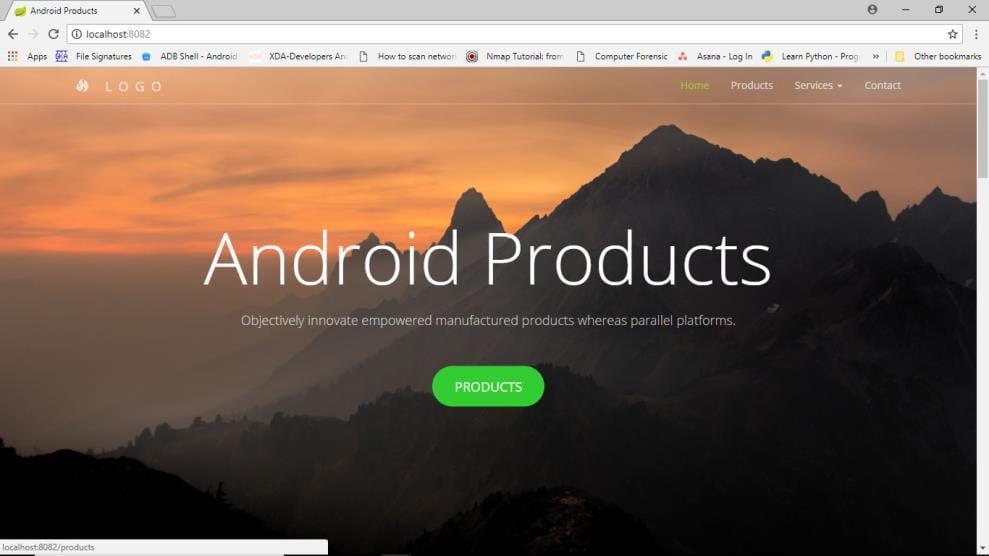
When you click the Products button, you will be redirected to the Keycloak login screen. Enter your username and password.
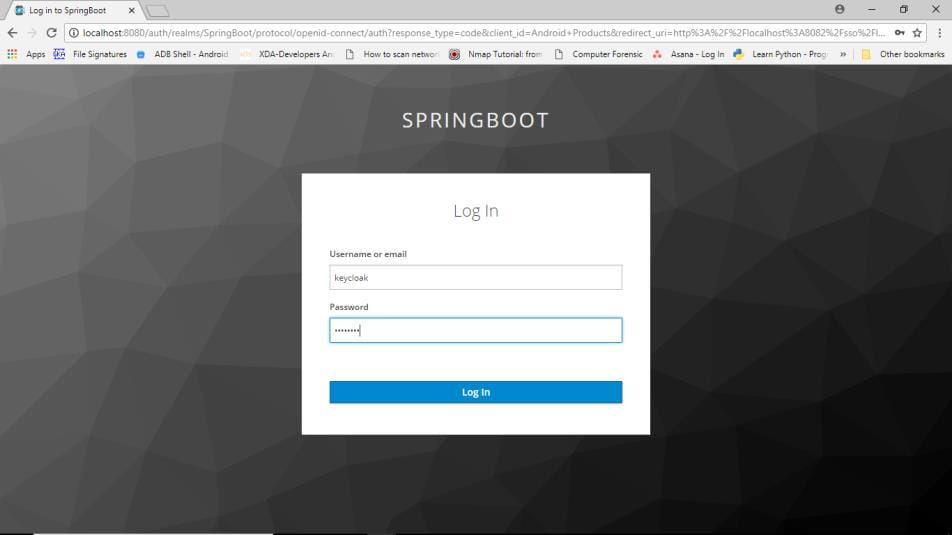
After successful authentication, you will be redirected back to the application.
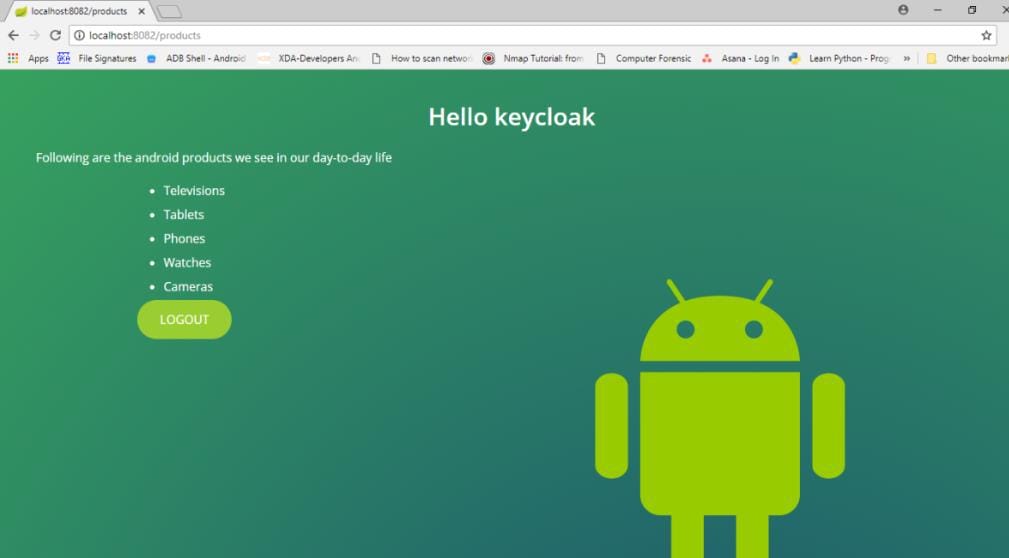
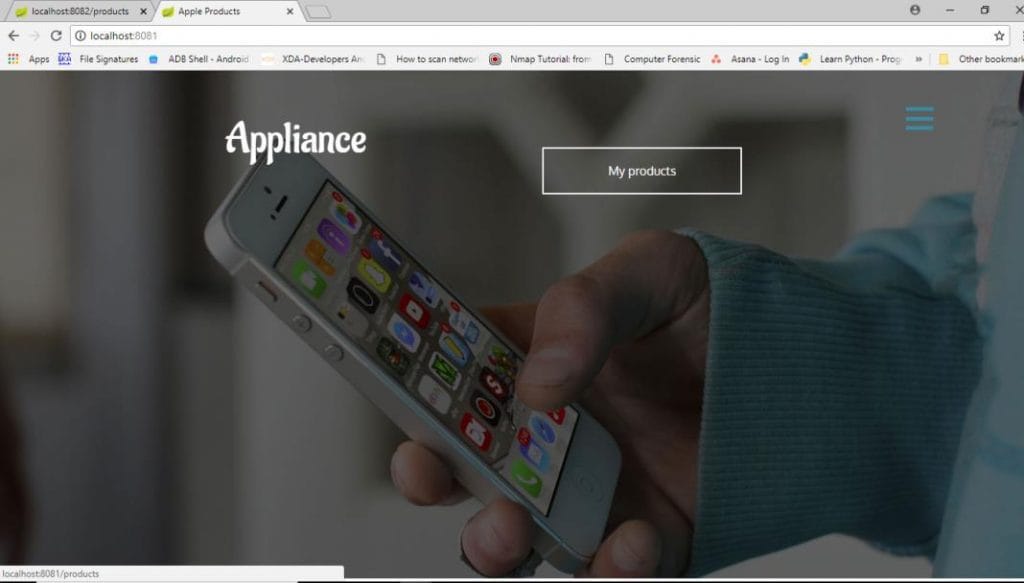
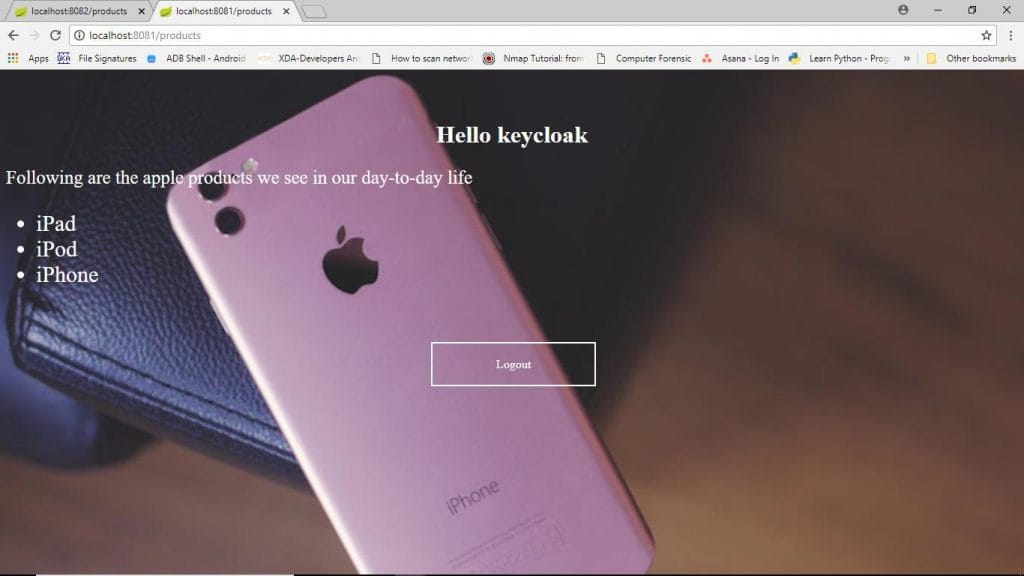
Now open a new tab and navigate to the second application's URL. Thanks to SSO, you will be redirected straight into the application — without being prompted to log in again.
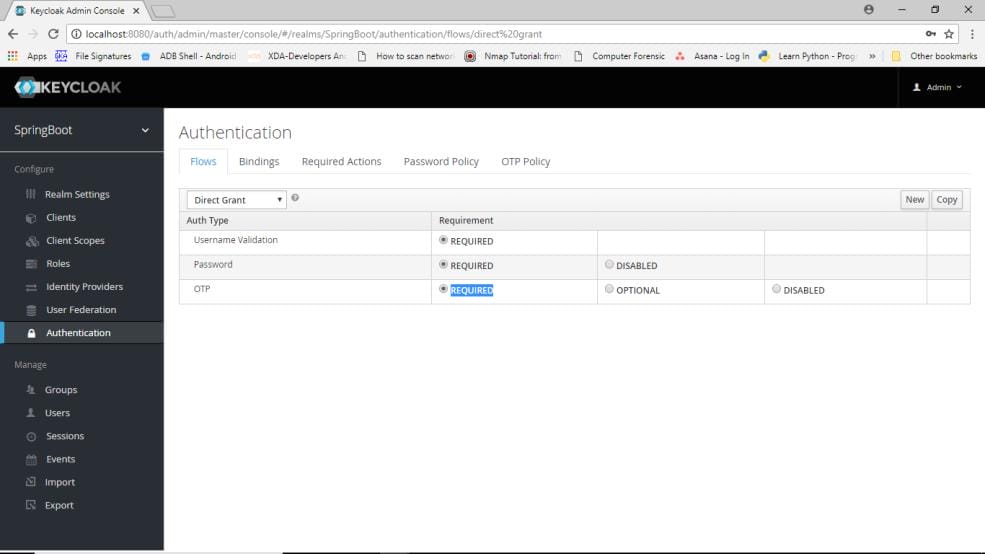
 Next, add an OTP authentication step. Go to Authentication → Flows → Direct Grant and set the OTP step to Required.
Next, add an OTP authentication step. Go to Authentication → Flows → Direct Grant and set the OTP step to Required.
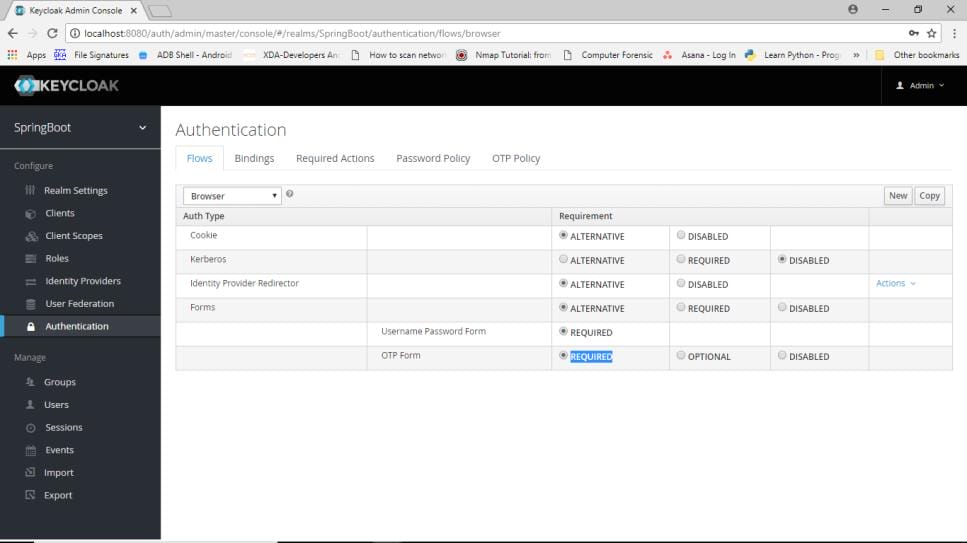
In the Browser Flow, also set OTP to Required.
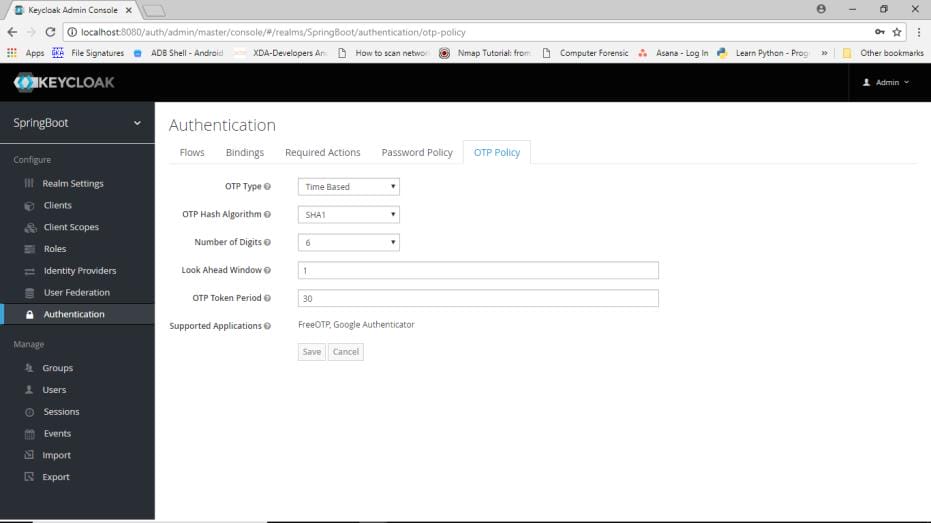
Under OTP Policy, you can configure hash algorithms, OTP time period, and other parameters.
Install FreeOTP or Google Authenticator on your mobile device.
Restart Keycloak, open the browser, and navigate to your application URL. After the Keycloak login screen, you will be presented with a QR code screen.
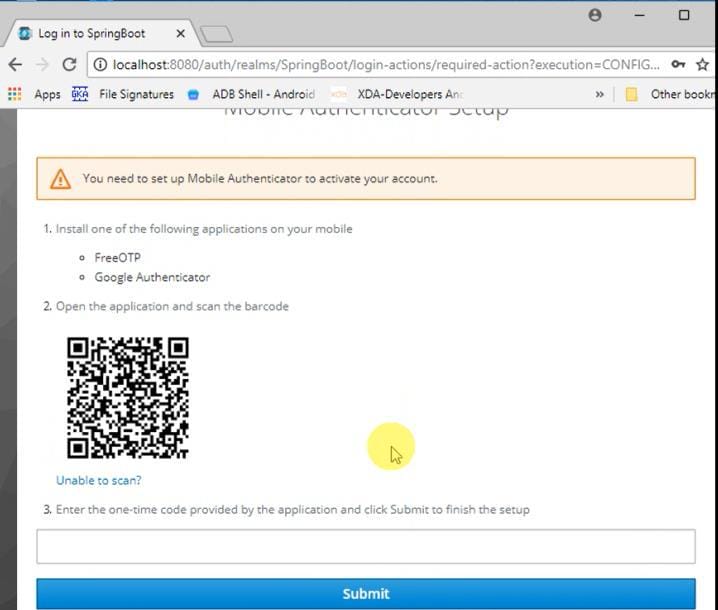
Scan the QR code with your authenticator app and enter the generated OTP. You will then be redirected into your application with multi-factor authentication fully enforced.
Written by

CoMakeIT
coMakeIT, a software product engineering company. We accelerate product innovation, modernize aging applications, and productize best practices into new software IP.
Contact