Introduction
Writing this article was motivated by multiple conversations with colleagues and clients sharing their thoughts on integrating security within their organizations and the challenges they faced. In this series of blogs, we want to inspire you and help you get started with your DevSecOps journey. This part aims to assist you with the non-technical aspects of DevSecOps and how they influence the organization and people. Future parts will dive into the technical aspects and how to apply them to adhere to Flow, Feedback, and Continuous Learning principles.
What is DevSecOps?
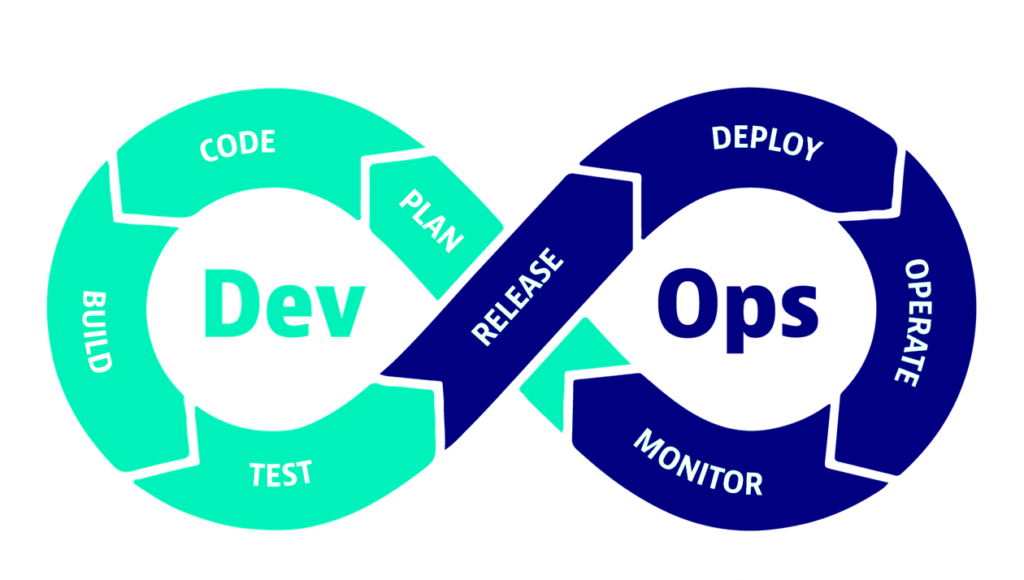
- DevOps
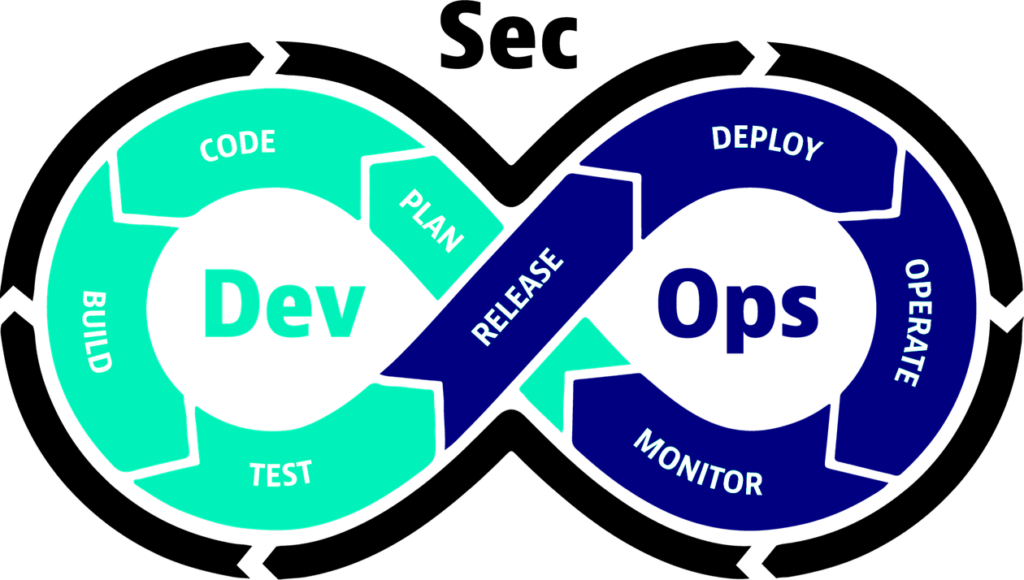
- How is security related to DevOps?
DevOps combines cultural philosophies, practices, and tools that increase an organization's ability to deliver applications and services at high velocity. With that high velocity, the old ways of securing your services are no longer sustainable.
The DevSecOps manifesto
The manifesto embodies the core principles of DevSecOps and aims to shift the perception of security within an organization.
- Leaning in over, Always Saying "No"
- Data & Security Science over Fear, Uncertainty, and Doubt
- Open Contribution & Collaboration over Security-Only Requirements
- Consumable Security Services with APIs over Mandated Security Controls & Paperwork
- Business-Driven Security Scores over Rubber Stamp Security
- Red & Blue Team Exploit Testing over Relying on Scans & Theoretical Vulnerabilities
- 24x7 Proactive Security Monitoring over Reacting after being Informed of an Incident
- Shared Threat Intelligence over Keeping Info to Ourselves
- Compliance Operations over Clipboards & Checklists
Source: DevSecOps.org
Why do you need DevSecOps?
- Traditional Security and the problem
- Flow, feedback, learning
The manifesto can help us understand some big-picture reasons for introducing DevSecOps, but you need to dig deeper to apply the context necessary for your organization.
Traditional Security often becomes a second-class citizen in the fast-paced world of DevOps. The way of working is not suitable for keeping up with the speed of the value streams. They lag and play the role of gatekeepers reducing the velocity of the value stream flows with long feedback loops and complicated learning journeys.
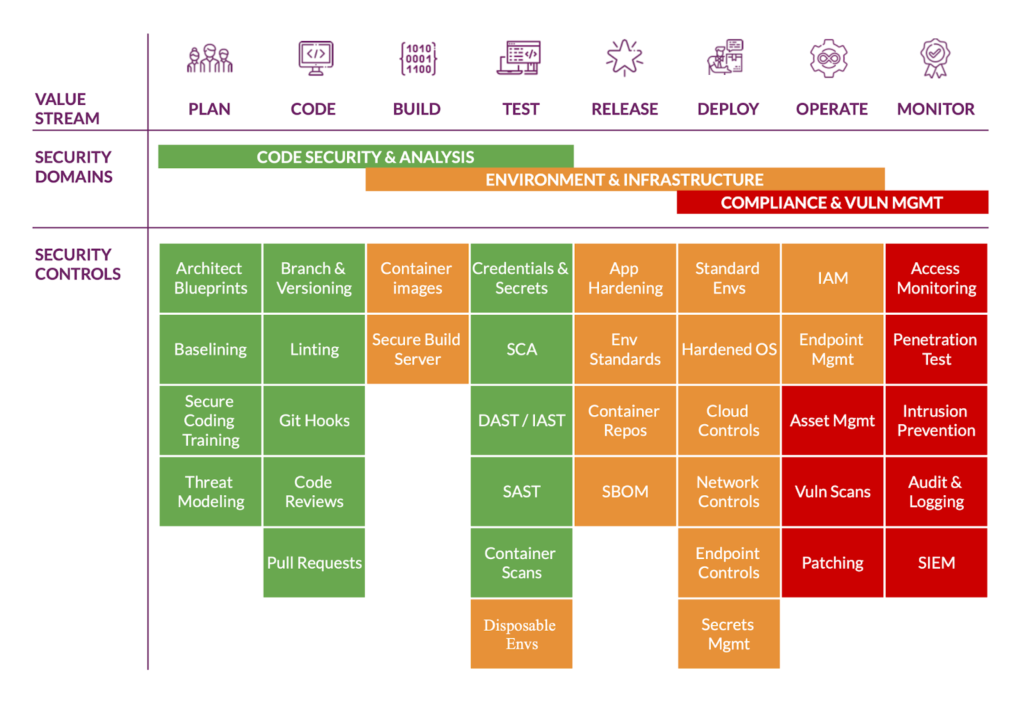
That is why we need a new approach to merge security into our value streams as a quality of our services. Integrating security quality gates in the early stages of the value stream will improve the flow by spreading the quality checks over the whole value stream. That, in turn, enables shorter feedback loops and provides learning opportunities in smaller and more digestible pieces.
With bite-size pieces, we make self-service, iteration, and incremental changes much more straightforward and lower the risk of those changes. A faster pace, less risk, and catching defects in the early stages bring more cost savings.
Ultimately, each organization will have its reasons, which might not work or make sense for another organization. The journey needs to be tailor-made for your needs.
How to start it up?
- Embrace the service
- Integrate security as a quality
- Gather your champions
The "Why" from the previous section can help you set a direction and scope of the "How" of setting up a DevSecOps program. It is paramount that the organization is on board with the upcoming transformation.
Embrace - Our job is not just to 'write code,' but it is 'run a service.'
A change in mindset is necessary, and existing Security teams need to step up and embrace Security as a Service rather than the Overseer approach. Most of the time, the Security Team needs to have the necessary context to assess the findings their tools generate. Allow the teams with that context to consume your findings and evaluate them.
Integrate Security as code into pipelines; start with running parallel tests that do not break or stop the pipeline but give feedback to the team. Gather the results and form your metrics and tracking KPIs
Find a balance between security, compliance, and speed of delivery, and build protection into the platforms and pipelines.
Gather people interested in security and create a Security Champions program, allocate time to talk about security and the unique solutions they come up with, and enable them to share their knowledge.
Next steps
In our upcoming posts, we will dive deeper into the technical aspects and security capabilities you can implement in your value streams. We would love to hear from you on which part of the value stream you want to hear first; send an email to fchyla@xebia.com with your suggestions.
Written by

Filip Chyla
"By failing to prepare, you are prepared to fail." Enable the business to grow securely and productively. Have a direction and start walking; you can continually realign. Help team members find their path and facilitate their journey. If you want to get far, go together. I am purple; I enjoy being on both sides of security. You need to know where to dig the trench or put the wall, and to do that, you need to know your weak points. I am always asking where we can set up the next layer.
Our Ideas
Explore More Blogs

Doomtenna: From Meshtastic to MeshCore
For the past few years we have been running Meshtastic, but recently, in January 2026, we made the switch to MeshCore.
Thomas de Ruiter

Where the GitHub Copilot Extension Points Break Governance
A lot of the recent additions to the GitHub Copilot ecosystem add real value for individual developers, yet they also expand the security surface that...
Rob Bos
Contact


